Data Protection/Recovery Strategy - Category
1. The Data Backup and Data Protection categories includes the following:
  (a) Data Backups
(b) Replication (c) Mirroring (d) Resilient Storage Implementation
(e) Cloud-based Disaster Recovery
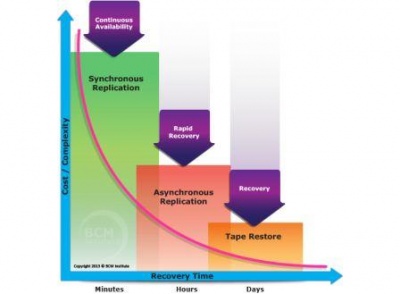
Note (1): Replication
Note (2): Synchronous Replication means that the application will receive simultaneous confirmations for data written simultaneously to either disks or locations. Note (3): Asynchronous Replication means that the application will receive a confirmation from the primary write first, and the secondary write later, as the secondary write might be to an alternate site located a hundred kilometres away; thus, the confirmation of the second write is going to take longer time. The reason for the selection of asynchronous replication option is to minimize the impact on the performance of the primary application (do not need to wait for the secondary write before proceeding) as this machine is usually machine-critical. Note (4): In extending the options of synchronous replication and asynchronous replication, there three are possible level of implementation:
Related Terms: Disaster Recovery Strategy

| ||||||||
2. Statutory requirements to manage personal data in a manner that does not threaten or disadvantage the person to whom it refers.

(Source: Business Continuity Institute - BCI)
